
FBI Taps Apple Push Logs To Read Signal
A court case shows the FBI using Apple’s push notification database to reconstruct Signal messages on iPhones and secure terrorism convictions, exposing a quiet surveillance vector.

A court case shows the FBI using Apple’s push notification database to reconstruct Signal messages on iPhones and secure terrorism convictions, exposing a quiet surveillance vector.

Diablo II: Resurrected PTR 3.2 rolls out with Warlock balance changes and refreshed Terror Zones, inviting players to test and provide feedback.
2026-04-11

Researchers report a shared brain activity fingerprint across five psychedelic drugs, revealing converging effects on connectivity, entropy and key networks that may explain both hallucinations and therapeutic potential.
2026-04-11

Microsoft is giving Windows 11 testers a built‑in way to unlock experimental features, replacing ViVeTool hacks and tightening control of the Fix Windows 11 effort.
2026-04-11

Utah now has the most active measles outbreak in the U.S., with more than 121 reported cases in recent weeks, surpassing states such as South Carolina and triggering aggressive public health containment measures.
2026-04-11

Researchers report that a low‑cost, already approved drug may reduce core autism symptoms in early trials, opening a path to rapid repurposing far beyond leucovorin.
2026-04-11

A CDC analysis on Covid vaccine benefits was delayed after concerns over its methods, raising fresh alarms over political interference in federal public health research.
2026-04-11

Microsoft is changing how Windows Insider channels receive new features, aiming for more predictable rollouts even as the program’s layered structure remains complex for testers.
2026-04-11

Pokemon Center is introducing an early access preorder window for customers who subscribe to its marketing newsletter, adding staggered availability before general sales.
2026-04-11
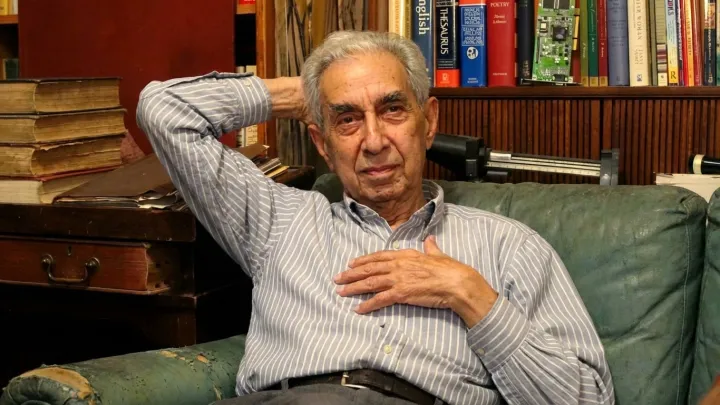
Thomas S. Langner, a leader of the Midtown Manhattan Study, showed how mental disorders track closely with socioeconomic inequality and reshaped public health thinking.
2026-04-11

A once‑feared Victorian infection is resurging, sending up to 90 percent of patients to hospital and exposing gaps in vaccination, surveillance and public‑health capacity.
2026-04-10